OWASP® Cornucopia 1.0 Mobile App Edition - Threat Modeling Cards
OWASP® Cornucopia 1.0 Mobile App Edition - Threat Modeling Cards is backordered and will ship as soon as it is back in stock.
Description
Description
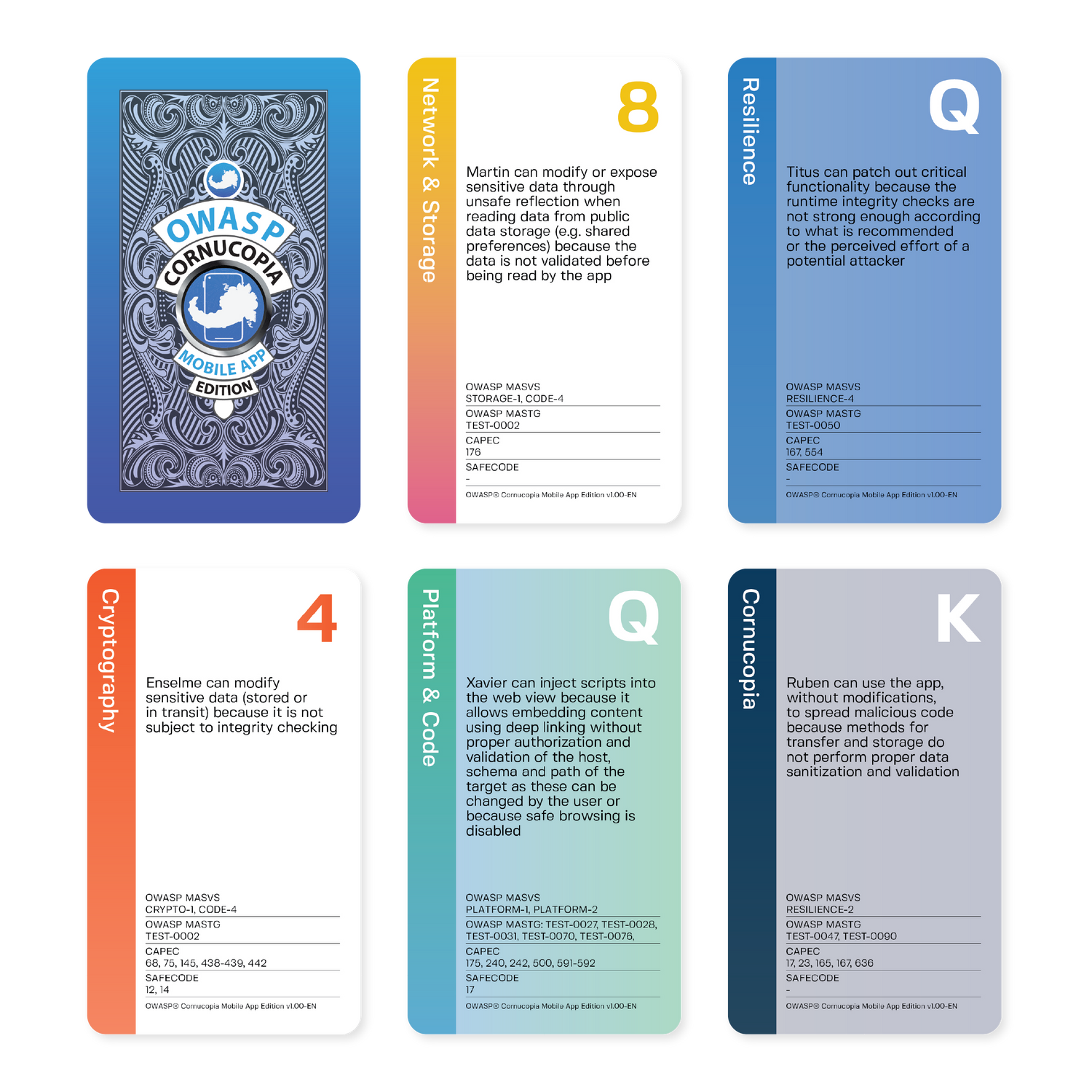
The Mobile App Edition is the second Cornucopia deck specifically for threat modeling mobile applications and adheres to the same principles and game rules as the original OWASP Cornucopia. This edition is aligned with OWASP Mobile Application Security Verification Standard (MASVS v2.0) and OWASP Mobile Application Security Testing Guide (MASTG) v1.7.
Key Features:
- MASVS Mapping: Designed to align with the latest MASVS and MASTG standards.
- Reliably Fun - consistent with Elevation of Privilege - and Hearts! Simultaneously competitive and collaborative, due to it's playful and inclusive gameplay.
- Platform and technology-agnostic - useful for everyone from PHP hackers, through Java wranglers, to PhD security experts
- Convenient tarot size - matching our collection of tarot sized threat modeling games
OWASP is a registered trademark of the OWASP Foundation.
Bulk Pricing
Bulk Pricing
Automatically applied at checkout:
| Buy | Discount |
|---|---|
| 5 or more decks | 5% off |
| 10 or more decks | 10% off |
| 20 or more decks | 20% off |
| 30 or more decks | 30% off |
Outcome
Outcome
Identify work that needs doing earlier in the project lifecycle. Defuse difficult relationships. Build trust. Bring teams together in peace and harmony.
Made by Agile Stationery
Made by Agile Stationery
Experts in delivering the right kind of conversations. Slick cards in robust boxes. The best there is outside the casinos.
Specifications
Specifications
-
SuitsPlatform & Code, Authentication & Authorization, Network & Storage, Resilience, Cryptography, Cornucopia
-
# Cards
-
Created by
Try a branded version
Try a branded version
If you'd like to encourage the use of this technique within your team or organisation, a branded deck is a great way to demonstrate your support and commitment to the process.
Quick Guide to Playing Cornucopia
1. Set the Scene: Pick a feature or app. Bring visuals (diagrams, stories). Gather 3 to 6 people including devs, testers, product folks, and ideally someone with security knowledge.
2. Deal the Cards: Shuffle the deck. Remove Jokers and low-numbered Cornucopia cards (2 to 4s). Deal the rest evenly.
3. Start Playing: Take turns playing cards. Stick to the same suit if possible. Read your card aloud and say how the threat might apply, no need to solve it yet. Highest card of the suit wins, unless trumped by a Cornucopia card. Winner starts the next round.
4. Score: +1 for a valid threat, +1 if your card wins the round. Most points wins.
5. Wrap-Up: Review threats, map to security standards, and turn them into backlog items.
Tip: have someone take notes for later use.